From Dark Reading:
Small Budgets Cripple Cybersecurity Efforts of Local Governments
"A survey of local government chief information officers finds that insufficient funding for cybersecurity is the biggest obstacle in achieving high levels of cyber safety.
Inadequate budgets are the largest obstacle for local government chief information officers in obtaining the highest level of cybersecurity for their organization, according to a survey released today by the International City/County Management Association."
The purpose of this blog is to help small-medium businesses (SMB's) deal effectively with their unique cyber security needs. With over 15 years experience in IT and cyber security I will show SMB's how they can leverage their limited resources to develop effective cyber defenses to the most common threats using information security best practices and no/low cost tools.
LinkedIn: http://www.linkedin.com/in/ecissorsky/
Twitter: @ecissorsky
Thursday, May 4, 2017
Google Docs Phishing Attack Abuses Legitimate Third-Party Sharing
From Dark Reading:
Google Docs Phishing Attack Abuses Legitimate Third-Party Sharing
"Phishing messages appear nearly identical to legitimate requests to share Google documents, because in many ways, they are.
Google users today were hit with an extremely convincing phishing spree launched by attackers who manipulated Google Docs' legitimate third-party sharing mechanism."
Google Docs Phishing Attack Abuses Legitimate Third-Party Sharing
"Phishing messages appear nearly identical to legitimate requests to share Google documents, because in many ways, they are.
Google users today were hit with an extremely convincing phishing spree launched by attackers who manipulated Google Docs' legitimate third-party sharing mechanism."
Tinder orders researcher to remove dataset of 40,000 profile pictures
From Sophos Naked Security:
Tinder orders researcher to remove dataset of 40,000 profile pictures
"Following a privacy kerfluffle, Tinder told a developer to remove a dataset of 40,000 of its users’ images that he had published in six downloadable zip files and released under a CC0: Public Domain License.
The dataset was called People of Tinder.
The developer, Stuart Colianni, who not-so-charmingly referred to the Tinder users as “hoes” in his source code, was using the images to train artificial intelligence."
Tinder orders researcher to remove dataset of 40,000 profile pictures
"Following a privacy kerfluffle, Tinder told a developer to remove a dataset of 40,000 of its users’ images that he had published in six downloadable zip files and released under a CC0: Public Domain License.
The dataset was called People of Tinder.
The developer, Stuart Colianni, who not-so-charmingly referred to the Tinder users as “hoes” in his source code, was using the images to train artificial intelligence."
Concern mounts at Indian ID scheme as portals ‘leak’ 100m people’s details
From Sophos Naked Security:
Concern mounts at Indian ID scheme as portals ‘leak’ 100m people’s details
"The details of more than 100m Indians’ Aadhaar ID cards have leaked from four government portals, according to a report from the Centre for Internet and Society (CIS).
Concern mounts at Indian ID scheme as portals ‘leak’ 100m people’s details
"The details of more than 100m Indians’ Aadhaar ID cards have leaked from four government portals, according to a report from the Centre for Internet and Society (CIS).
Based on the numbers available on the websites looked at, [the] estimated number of Aadhaar numbers leaked through these four portals could be around 130-135 million"
NSA collected records of 151m Americans – but wait, didn’t bulk collection stop three years ago?
From Sophos Naked Security:
NSA collected records of 151m Americans – but wait, didn’t bulk collection stop three years ago?
"You remember the NSA’s bulk phone data collection program, right?
As in, the one that Congress cut the funding for in 2014? The one that wasn’t authorized by Section 215 of the Patriot Act after all, as a court unanimously ruled in 2015? … but which got extended anyway?
Boy, did it get extended, and how. It’s still chugging along just fine."
NSA collected records of 151m Americans – but wait, didn’t bulk collection stop three years ago?
"You remember the NSA’s bulk phone data collection program, right?
As in, the one that Congress cut the funding for in 2014? The one that wasn’t authorized by Section 215 of the Patriot Act after all, as a court unanimously ruled in 2015? … but which got extended anyway?
Boy, did it get extended, and how. It’s still chugging along just fine."
Update: Google Doc phishing story takes some bizarre turns
From Sophos Naked Security:
Update: Google Doc phishing story takes some bizarre turns
"Since news began circulating last night of a phishing campaign parading around as Google Doc access links, the tale has taken strange twists and turns.
A self-described graduate student claims he was behind the blast of emails, and that they were part of a test for a school project, not a phishing attack. But according to the university he claims to be enrolled at, he’s not a student there."
Update: Google Doc phishing story takes some bizarre turns
"Since news began circulating last night of a phishing campaign parading around as Google Doc access links, the tale has taken strange twists and turns.
A self-described graduate student claims he was behind the blast of emails, and that they were part of a test for a school project, not a phishing attack. But according to the university he claims to be enrolled at, he’s not a student there."
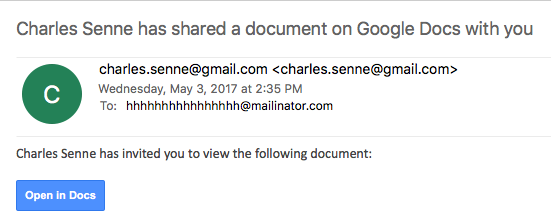
FYI - to help reduce the attack surface block:
hhhhhhhhhhhhhhhh @ mailinator . com
on your email system(s).
US-CERT Alert: Microsoft Ending Security Updates for Windows 10 version 1507
From US-CERT:
Microsoft Ending Security Updates for Windows 10 version 1507
"After May 9, 2017, devices running Windows 10 version 1507 will no longer receive security updates."
Microsoft Ending Security Updates for Windows 10 version 1507
"After May 9, 2017, devices running Windows 10 version 1507 will no longer receive security updates."
US-CERT Alert: Cisco Releases Security Updates
From US-CERT:
Cisco Releases Security Updates
"Cisco has released updates to address vulnerabilities affecting multiple products. A remote attacker could exploit some of these vulnerabilities to take control of an affected system."
Cisco Releases Security Updates
"Cisco has released updates to address vulnerabilities affecting multiple products. A remote attacker could exploit some of these vulnerabilities to take control of an affected system."
Wednesday, May 3, 2017
OAUTH phishing against Google Docs ? beware!
From SANS ISC:
OAUTH phishing against Google Docs ? beware!
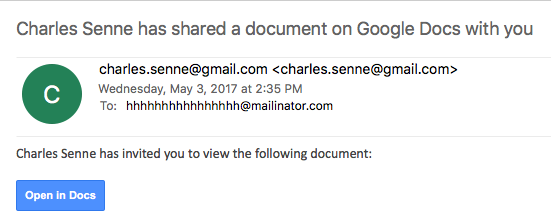
We got several reports (thanks to Seren Thompson, Tahir Khan and Harry Vann) about OAUTH phishing attacks against Google users. The phishing attack arrives, of course, as an e-mail where it appears that a user (potentially even one on your contact list, so it looks very legitimate) has shared a document.
An image of such an e-mail is shown below:
OAUTH phishing against Google Docs ? beware!
We got several reports (thanks to Seren Thompson, Tahir Khan and Harry Vann) about OAUTH phishing attacks against Google users. The phishing attack arrives, of course, as an e-mail where it appears that a user (potentially even one on your contact list, so it looks very legitimate) has shared a document.
An image of such an e-mail is shown below:
Cyberwarfare Can Help Unravel NKorea Nuke Threat
From Newsmax:
Cyberwarfare Can Help Unravel NKorea Nuke Threat
"The U.S. must bone up on cyberwar strategies to battle North Korea strongman Kim Jong-un's growing nuclear threats, Jed Babbin, former deputy undersecretary of defense in the George H.W. Bush administration, tells Newsmax TV."
Cyberwarfare Can Help Unravel NKorea Nuke Threat
"The U.S. must bone up on cyberwar strategies to battle North Korea strongman Kim Jong-un's growing nuclear threats, Jed Babbin, former deputy undersecretary of defense in the George H.W. Bush administration, tells Newsmax TV."
How does USB Killer v3 damage devices through their USB connections?
From SearchSecurity:
How does USB Killer v3 damage devices through their USB connections?
"USB Killer devices, with the ability to destroy systems via a USB input, are available and inexpensive. Expert Nick Lewis explains how they work and how to defend against this threat."
How does USB Killer v3 damage devices through their USB connections?
"USB Killer devices, with the ability to destroy systems via a USB input, are available and inexpensive. Expert Nick Lewis explains how they work and how to defend against this threat."
Facebook to Add 3,000 Workers to Fight Streaming of Live Violence
From Newsmax:
Facebook to Add 3,000 Workers to Fight Streaming of Live Violence
"Facebook Inc will add 3,000 people over the next year to monitor reports of inappropriate material on the social media network and removing videos such as murders and suicides, Chief Executive Officer Mark Zuckerberg said on Wednesday.
Zuckerberg, the company's co-founder, said in a Facebook post the workers will be in addition to the 4,500 people who already review posts that may violate its terms of service."
Facebook to Add 3,000 Workers to Fight Streaming of Live Violence
"Facebook Inc will add 3,000 people over the next year to monitor reports of inappropriate material on the social media network and removing videos such as murders and suicides, Chief Executive Officer Mark Zuckerberg said on Wednesday.
Zuckerberg, the company's co-founder, said in a Facebook post the workers will be in addition to the 4,500 people who already review posts that may violate its terms of service."
DARPA Is Planning to Hack the Human Brain to Let Us “Upload” Skills
From Futurism:
DARPA Is Planning to Hack the Human Brain to Let Us “Upload” Skills
"In March 2016, DARPA — the U.S. military’s “mad science” branch — announced their Targeted Neuroplasticity Training (TNT) program. The TNT program aims to explore various safe neurostimulation methods for activating synaptic plasticity, which is the brain’s ability to alter the connecting points between neurons — a requirement for learning. DARPA hopes that building up that ability by subjecting the nervous system to a kind of workout regimen will enable the brain to learn more quickly."
DARPA Is Planning to Hack the Human Brain to Let Us “Upload” Skills
"In March 2016, DARPA — the U.S. military’s “mad science” branch — announced their Targeted Neuroplasticity Training (TNT) program. The TNT program aims to explore various safe neurostimulation methods for activating synaptic plasticity, which is the brain’s ability to alter the connecting points between neurons — a requirement for learning. DARPA hopes that building up that ability by subjecting the nervous system to a kind of workout regimen will enable the brain to learn more quickly."
Netgear Patches RCE Flaws in Routers, Switches
From SecurityWeek:
Netgear Patches RCE Flaws in Routers, Switches
"Netgear recently informed customers that it has released firmware updates for some of its routers and switches to address remote code execution and other types of vulnerabilities.
Netgear announced the launch of a bug bounty program in early January and the company has been regularly publishing security advisories and notifications over the past months. The firm has been offering between $150 and $15,000 for responsibly disclosed vulnerabilities, and it already claims to have rewarded more than 150 bug reports."
Netgear Patches RCE Flaws in Routers, Switches
"Netgear recently informed customers that it has released firmware updates for some of its routers and switches to address remote code execution and other types of vulnerabilities.
Netgear announced the launch of a bug bounty program in early January and the company has been regularly publishing security advisories and notifications over the past months. The firm has been offering between $150 and $15,000 for responsibly disclosed vulnerabilities, and it already claims to have rewarded more than 150 bug reports."
Travel Tech Giant Sabre Investigating Data Breach
From SecurityWeek:
Travel Tech Giant Sabre Investigating Data Breach
"Travel technology giant Sabre revealed that it has launched an investigation after detecting unauthorized access to sensitive information processed through one of its systems.
Southlake, Texas-based Sabre said in an SEC filing this week that it’s “investigating an incident involving unauthorized access to payment information contained in a subset of hotel reservations processed through the Sabre Hospitality Solutions SynXis Central Reservation system.”
Travel Tech Giant Sabre Investigating Data Breach
"Travel technology giant Sabre revealed that it has launched an investigation after detecting unauthorized access to sensitive information processed through one of its systems.
Southlake, Texas-based Sabre said in an SEC filing this week that it’s “investigating an incident involving unauthorized access to payment information contained in a subset of hotel reservations processed through the Sabre Hospitality Solutions SynXis Central Reservation system.”
WordPress Attacks Powered by Router Botnet Drop Rapidly
From SecurityWeek:
WordPress Attacks Powered by Router Botnet Drop Rapidly
"A botnet powered by compromised home routers has been apparently shut down. It is unclear if the botnet operators decided to pull the plug on their operation or if the disruption was caused by law enforcement.
Security firm Wordfence warned last month that tens of thousands of vulnerable routers from dozens of ISPs worldwide had been abused for brute-force and other types of attacks aimed at WordPress websites."
WordPress Attacks Powered by Router Botnet Drop Rapidly
"A botnet powered by compromised home routers has been apparently shut down. It is unclear if the botnet operators decided to pull the plug on their operation or if the disruption was caused by law enforcement.
Security firm Wordfence warned last month that tens of thousands of vulnerable routers from dozens of ISPs worldwide had been abused for brute-force and other types of attacks aimed at WordPress websites."
New Cerber Ransomware Variant Emerges
From SecurityWeek:
New Cerber Ransomware Variant Emerges
"A new variant of the Cerber ransomware has emerged over the past month, featuring multipart arrival vectors and refashioned file encryption routines, TrendMicro security researchers warn.
An active threat for over a year, Cerber managed to climb at the top of ransomware charts earlier this year, accounting for 87% of attacks in the first quarter of 2017. The rise was fueled mainly by a major decrease in Locky attacks, but Cerber’s popularity among cybercriminals also helped."
New Cerber Ransomware Variant Emerges
"A new variant of the Cerber ransomware has emerged over the past month, featuring multipart arrival vectors and refashioned file encryption routines, TrendMicro security researchers warn.
An active threat for over a year, Cerber managed to climb at the top of ransomware charts earlier this year, accounting for 87% of attacks in the first quarter of 2017. The rise was fueled mainly by a major decrease in Locky attacks, but Cerber’s popularity among cybercriminals also helped."
Google Patches More Critical Flaws in Android Mediaserver
From SecurityWeek:
Google Patches More Critical Flaws in Android Mediaserver
"Google this week announced the contents of the May 2017 Android security patches, revealing that six Critical Remote Code Execution (RCE) flaws were addressed in the Mediaserver component.
Over the past couple of years, Mediaserver emerged as one of the most vulnerable Android components, after a Critical RCE bug dubbed Stagefright was said to affect 950 million devices. Detailed in July 2015, the vulnerability encouraged Google to issue monthly security updates for Android."
Google Patches More Critical Flaws in Android Mediaserver
"Google this week announced the contents of the May 2017 Android security patches, revealing that six Critical Remote Code Execution (RCE) flaws were addressed in the Mediaserver component.
Over the past couple of years, Mediaserver emerged as one of the most vulnerable Android components, after a Critical RCE bug dubbed Stagefright was said to affect 950 million devices. Detailed in July 2015, the vulnerability encouraged Google to issue monthly security updates for Android."
Healthcare Breaches Hit All-Time High in 2016
From Dark Reading:
Healthcare Breaches Hit All-Time High in 2016
"More than 300 healthcare businesses reported data breaches in 2016, but a drop in leaked records put fewer Americans at risk.
A record-breaking 328 healthcare businesses reported data breaches in 2016, surpassing the record of 268 set one year prior. Healthcare records of about 16.6 million Americans were exposed due to hacks, lost or stolen devices, unauthorized disclosure, and other activity."
Healthcare Breaches Hit All-Time High in 2016
"More than 300 healthcare businesses reported data breaches in 2016, but a drop in leaked records put fewer Americans at risk.
A record-breaking 328 healthcare businesses reported data breaches in 2016, surpassing the record of 268 set one year prior. Healthcare records of about 16.6 million Americans were exposed due to hacks, lost or stolen devices, unauthorized disclosure, and other activity."
Verizon DBIR Shows Attack Patterns Vary Widely By Industry
From Dark Reading:
Verizon DBIR Shows Attack Patterns Vary Widely By Industry
"It's not always the newest or the most sophisticated threat you need to worry about, Verizon's breach and security incident data for 2016 shows.
Among the many key takeaways in the 2017 edition Verizon’s annual Data Breach Investigations Report (DBIR), released Thursday, is that there are significant differences in why and how organizations across different industries are attacked."
Verizon DBIR Shows Attack Patterns Vary Widely By Industry
"It's not always the newest or the most sophisticated threat you need to worry about, Verizon's breach and security incident data for 2016 shows.
Among the many key takeaways in the 2017 edition Verizon’s annual Data Breach Investigations Report (DBIR), released Thursday, is that there are significant differences in why and how organizations across different industries are attacked."
Want to get your Android phone purring? Don’t install Full Optimizer
From Sophos Naked Security:
Want to get your Android phone purring? Don’t install Full Optimizer
"If you’re no fan of advertisements popping up on your device, you’ll want to avoid two apps in Google Play: Full Optimizer and Full Optimizer Lite. They deliver adware and don’t really do the things the developer claims."
Want to get your Android phone purring? Don’t install Full Optimizer
"If you’re no fan of advertisements popping up on your device, you’ll want to avoid two apps in Google Play: Full Optimizer and Full Optimizer Lite. They deliver adware and don’t really do the things the developer claims."
Powershelling with exploits
From SANS ISC:
Powershelling with exploits
Powershelling with exploits
US-CERT Alert: Google Releases Security Updates for Chrome
From US-CERT:
Google Releases Security Updates for Chrome
"Google has released Chrome version 58.0.3029.96 for Windows, Mac, and Linux. This version addresses a vulnerability that an attacker could exploit to cause a denial-of-service condition."
Google Releases Security Updates for Chrome
"Google has released Chrome version 58.0.3029.96 for Windows, Mac, and Linux. This version addresses a vulnerability that an attacker could exploit to cause a denial-of-service condition."
Tuesday, May 2, 2017
IBM Shipped Malware-Infected Flash Drives to Customers
From Databreach Today:
IBM Shipped Malware-Infected Flash Drives to Customers
"In a security alert, IBM is warning that it inadvertently shipped malware-infected USB flash drives to some of its storage hardware customers as well as to customers of some Lenovo-branded products."
IBM Shipped Malware-Infected Flash Drives to Customers
"In a security alert, IBM is warning that it inadvertently shipped malware-infected USB flash drives to some of its storage hardware customers as well as to customers of some Lenovo-branded products."
Facebook Engineer: Women's Codes Get Rejected More Than Male Peers
From Newsmax:
Facebook Engineer: Women's Codes Get Rejected More Than Male Peers
"Facebook has an apparent gender bias when it comes to programming.
Code written by female engineers at Facebook was rejected 35 percent more than code written by men according to findings uncovered last September by a longtime engineer at the company who gathered data on the subject, the Wall Street Journal reports. Screenshots of internal discussions on the matter were provided to the WSJ and people familiar with the findings spoke the newspaper."
Facebook Engineer: Women's Codes Get Rejected More Than Male Peers
"Facebook has an apparent gender bias when it comes to programming.
Code written by female engineers at Facebook was rejected 35 percent more than code written by men according to findings uncovered last September by a longtime engineer at the company who gathered data on the subject, the Wall Street Journal reports. Screenshots of internal discussions on the matter were provided to the WSJ and people familiar with the findings spoke the newspaper."
Super Free Music Player in Google Play is malware: a technical analysis
From Sophos Naked Security:
Super Free Music Player in Google Play is malware: a technical analysis
Take a good look at this find in Google Play. It goes by the name Super Free Music Player and has so far attracted between 5,000 and 10,000 downloads:

Super Free Music Player in Google Play is malware: a technical analysis
Take a good look at this find in Google Play. It goes by the name Super Free Music Player and has so far attracted between 5,000 and 10,000 downloads:

GE patches flaws allowing attackers to ‘disconnect power grid at will’
From Sophos Naked Security:
GE patches flaws allowing attackers to ‘disconnect power grid at will’
"Researchers have discovered a significant software flaw in the energy grid equipment sold by General Electric (GE) that could allow even lone attackers with limited resources to “disconnect sectors of the power grid at will”.
Until last week, this alarming sentence was little more than a one part of a placeholder for July’s Black Hat conference, advertising a session by three researchers from New York University."
GE patches flaws allowing attackers to ‘disconnect power grid at will’
"Researchers have discovered a significant software flaw in the energy grid equipment sold by General Electric (GE) that could allow even lone attackers with limited resources to “disconnect sectors of the power grid at will”.
Until last week, this alarming sentence was little more than a one part of a placeholder for July’s Black Hat conference, advertising a session by three researchers from New York University."
Fraudsters draining accounts with ‘SIM swaps’ – what to do
From Sophos Naked Security:
Fraudsters draining accounts with ‘SIM swaps’ – what to do
"Have you ever lost your mobile phone?
If so, you already know that your mobile provider will happily sell you a new phone and give you a brand new SIM card to activate the handset.
Lo and behold, when you fire up the new phone, it has your old number, so you don’t need to give all your friends and colleagues a new one."
Fraudsters draining accounts with ‘SIM swaps’ – what to do
"Have you ever lost your mobile phone?
If so, you already know that your mobile provider will happily sell you a new phone and give you a brand new SIM card to activate the handset.
Lo and behold, when you fire up the new phone, it has your old number, so you don’t need to give all your friends and colleagues a new one."
How does Exaspy spyware disguise itself on Android devices?
From SearchSecurity (subscription required):
How does Exaspy spyware disguise itself on Android devices?
"Exaspy spyware, which can access messages, video chats and more, was found on Android devices owned by executives. Expert Nick Lewis explains how Exaspy is able to avoid detection.
Researchers have discovered Android spyware called Exaspy being used to intercept phone-based communications on executives' devices, including phone calls, text messages, video chats and photos. Most mobile security scanners have not been able to detect the spyware. How does Exaspy disguise itself and evade detection?"
How does Exaspy spyware disguise itself on Android devices?
"Exaspy spyware, which can access messages, video chats and more, was found on Android devices owned by executives. Expert Nick Lewis explains how Exaspy is able to avoid detection.
Researchers have discovered Android spyware called Exaspy being used to intercept phone-based communications on executives' devices, including phone calls, text messages, video chats and photos. Most mobile security scanners have not been able to detect the spyware. How does Exaspy disguise itself and evade detection?"
Do Indicators of Compromise Matter? The Devil is in the Details
From Security Week:
Do Indicators of Compromise Matter? The Devil is in the Details
"Instead of Discounting Indicators of Compromise, it’s Time to Use Them More Effectively
The security industry has shifted from focusing on just signatures to include Indicators of Compromise (IoCs) as well. This is because in many ways IoCs are more portable, simplistic and compatible across many different detection platforms. However, during this shift IoCs have gotten a bum rap. It’s easy to see how this has happened – indicators can sometimes be just pieces of data without context. Security professionals are struggling to make sense of data, and wondering where to find real value as they strive to secure their environment."
Do Indicators of Compromise Matter? The Devil is in the Details
"Instead of Discounting Indicators of Compromise, it’s Time to Use Them More Effectively
The security industry has shifted from focusing on just signatures to include Indicators of Compromise (IoCs) as well. This is because in many ways IoCs are more portable, simplistic and compatible across many different detection platforms. However, during this shift IoCs have gotten a bum rap. It’s easy to see how this has happened – indicators can sometimes be just pieces of data without context. Security professionals are struggling to make sense of data, and wondering where to find real value as they strive to secure their environment."
Infosys to Hire 10,000 US Workers After Trump Targets Outsourcing Firms
Good news for American IT & other knowledge workers. From Newsmax:
Infosys to Hire 10,000 US Workers After Trump Targets Outsourcing Firms
"India-based IT services firm Infosys Ltd. said it plans to hire 10,000 U.S. workers in the next two years and open four technology centers in the United States, starting with a center this August in Indiana, the home state of U.S. Vice President Mike Pence.
The move comes at a time when Infosys and some of its Indian peers such as Tata Consultancy Services and Wipro Ltd. have become political targets in the United States for allegedly displacing U.S. workers' jobs by flying in foreigners on temporary visas to service their clients in the country."
Infosys to Hire 10,000 US Workers After Trump Targets Outsourcing Firms
"India-based IT services firm Infosys Ltd. said it plans to hire 10,000 U.S. workers in the next two years and open four technology centers in the United States, starting with a center this August in Indiana, the home state of U.S. Vice President Mike Pence.
The move comes at a time when Infosys and some of its Indian peers such as Tata Consultancy Services and Wipro Ltd. have become political targets in the United States for allegedly displacing U.S. workers' jobs by flying in foreigners on temporary visas to service their clients in the country."
How Cybercrooks Put the Beatdown on My Beats
From Krebs On Security:
How Cybercrooks Put the Beatdown on My Beats
"Last month Yours Truly got snookered by a too-good-to-be-true online scam in which some dirtball hijacked an Amazon merchant’s account and used it to pimp steeply discounted electronics that he never intended to sell. Amazon refunded my money, and the legitimate seller never did figure out how his account was hacked. But such attacks are becoming more prevalent of late as crooks increasingly turn to online crimeware services that make it a cakewalk to cash out stolen passwords."
How Cybercrooks Put the Beatdown on My Beats
"Last month Yours Truly got snookered by a too-good-to-be-true online scam in which some dirtball hijacked an Amazon merchant’s account and used it to pimp steeply discounted electronics that he never intended to sell. Amazon refunded my money, and the legitimate seller never did figure out how his account was hacked. But such attacks are becoming more prevalent of late as crooks increasingly turn to online crimeware services that make it a cakewalk to cash out stolen passwords."
Blind Trust in Email Could Cost You Your Home
From Krebs On Security:
Blind Trust in Email Could Cost You Your Home
"The process of buying or selling a home can be extremely stressful and complex, but imagine the stress that would boil up if — at settlement — your money was wired to scammers in another country instead of to the settlement firm or escrow company. Here’s the story about a phishing email that cost a couple their home and left them scrambling for months to recover hundreds of thousands in cash that went missing."
Blind Trust in Email Could Cost You Your Home
"The process of buying or selling a home can be extremely stressful and complex, but imagine the stress that would boil up if — at settlement — your money was wired to scammers in another country instead of to the settlement firm or escrow company. Here’s the story about a phishing email that cost a couple their home and left them scrambling for months to recover hundreds of thousands in cash that went missing."
Infographic: 7 Ways Hackers Look To Exploit Your State & Local Governments
PDF format infographic from CoreSecurity:
7 Ways Hackers Look To Exploit Your State & Local Governments
7 Ways Hackers Look To Exploit Your State & Local Governments
Hacking is now so common that even small nations are doing it
From McClatchy:
Hacking is now so common that even small nations are doing it
"Russian state hackers get the headlines, but nations across the globe are pouring money into cyber espionage units, a development, security experts say, that is allowing smaller nations to close the espionage gap without the satellites or tech muscle of big nations.
“It’s very inexpensive. It’s very efficient,” said John Hultquist, a cyber espionage analyst who’s studied the growth of hacking among smaller nations for iSight Partners, a division of FireEye, a Milpitas, California, cybersecurity firm."
Hacking is now so common that even small nations are doing it
"Russian state hackers get the headlines, but nations across the globe are pouring money into cyber espionage units, a development, security experts say, that is allowing smaller nations to close the espionage gap without the satellites or tech muscle of big nations.
“It’s very inexpensive. It’s very efficient,” said John Hultquist, a cyber espionage analyst who’s studied the growth of hacking among smaller nations for iSight Partners, a division of FireEye, a Milpitas, California, cybersecurity firm."
US-CERT Alert: Intel Firmware Vulnerability
From US-CERT:
Intel Firmware Vulnerability
"Intel has released recommendations to address a vulnerability in the firmware of the following Intel products: Active Management Technology, Standard Manageability, and Small Business Technology, firmware versions 6.x, 7.x, 8.x 9.x, 10.x, 11.0, 11.5, and 11.6. This vulnerability does not affect Intel-based consumer PCs. An attacker could exploit this vulnerability to take control of an affected system."
Intel Firmware Vulnerability
"Intel has released recommendations to address a vulnerability in the firmware of the following Intel products: Active Management Technology, Standard Manageability, and Small Business Technology, firmware versions 6.x, 7.x, 8.x 9.x, 10.x, 11.0, 11.5, and 11.6. This vulnerability does not affect Intel-based consumer PCs. An attacker could exploit this vulnerability to take control of an affected system."
Monday, May 1, 2017
Iranian Hackers Exploit Recent Office 0-Day in Attacks: Report
Glad to see they are putting the billion plus cash payment the US gave them last year is being put to good use. </sarcasm>
From SecurityWeek:
Iranian Hackers Exploit Recent Office 0-Day in Attacks: Report
"A recently patched vulnerability in Microsoft Office has been abused by Iranian threat actors in attacks against Israeli organizations, researchers from security firm Morphisec reveal.
Carried out between April 19 and April 24, 2017, the politically-motivated, targeted campaign was leveraging the CVE-2017-0199 vulnerability in Office that Microsoft patched earlier this month, after it had been already abused in live attacks. Because many organizations failed to apply the patch, however, the vulnerability continues to offer a viable attack surface."
From SecurityWeek:
Iranian Hackers Exploit Recent Office 0-Day in Attacks: Report
"A recently patched vulnerability in Microsoft Office has been abused by Iranian threat actors in attacks against Israeli organizations, researchers from security firm Morphisec reveal.
Carried out between April 19 and April 24, 2017, the politically-motivated, targeted campaign was leveraging the CVE-2017-0199 vulnerability in Office that Microsoft patched earlier this month, after it had been already abused in live attacks. Because many organizations failed to apply the patch, however, the vulnerability continues to offer a viable attack surface."
Microsoft Turns Off Wi-Fi Sense After Risk Revealed
From DataBreach Today:
Microsoft Turns Off Wi-Fi Sense After Risk Revealed
"Remember Microsoft's Wi-Fi Sense? The Windows 10 feature shared encrypted passwords to Wi-Fi networks with user's Skype and Outlook contacts. The idea was that friends could then easily connect to other networks without needing login details. But it raised privacy and security concerns."
Microsoft Turns Off Wi-Fi Sense After Risk Revealed
"Remember Microsoft's Wi-Fi Sense? The Windows 10 feature shared encrypted passwords to Wi-Fi networks with user's Skype and Outlook contacts. The idea was that friends could then easily connect to other networks without needing login details. But it raised privacy and security concerns."
Hack of new season of ‘Orange is the New Black’ portends a looming TV crisis
From McClatchy:
Hack of new season of ‘Orange is the New Black’ portends a looming TV crisis
"After stealing and releasing 10 episodes of the fifth season of the Netflix series “Orange is the New Black” a month before its official premiere, a shadowy hacking group now is threatening to release shows by four other networks unless the networks’ pay a ransom.
It’s a sign of things to come. The future is being hacked, and there’s no certainty where it might end. In today’s digital world, hackers can steal an ever-growing number of secrets."
Hack of new season of ‘Orange is the New Black’ portends a looming TV crisis
"After stealing and releasing 10 episodes of the fifth season of the Netflix series “Orange is the New Black” a month before its official premiere, a shadowy hacking group now is threatening to release shows by four other networks unless the networks’ pay a ransom.
It’s a sign of things to come. The future is being hacked, and there’s no certainty where it might end. In today’s digital world, hackers can steal an ever-growing number of secrets."
POLICE PHONE SCAM ALERT
Yesterday I received a call from someone pretending to be Det. Garry McFadden from the Charlotte-Mecklenberg PD. The caller left a message stating there was a criminal charge filed against me & I would be arrested if I didn't call back within 24-48 hours.
I returned the call several times. Each time the phone rang three (3) times before giving me a message stating "The person you are calling has a voicemail box that has not been set up." This morning I spoke with a person with the CMPD. They confirmed that Det. Garry McFadden was a detective in their department but has retired because he has a show on Investigation Discovery. The person indicated this is a scam and forwarded me to their Fraud Dept.
Earlier today I spoke with the person claiming to be Det. McFadden. He went into a high pressure spiel about charges being filed if I did not take care of this matter immediately. I confirmed his name & asked if he was still with the CMPD. The male stated he was. I then asked if he was the same Det. McFadden who now has a show on ID. He said that was him & he is now a private investigator. At this point I asked if he was a private investigator & no longer associated with the CMPD why was he misrepresenting himself as an officer of the law? The male did not answer this question, instead he stated that he had "talked to some people up in my area." I asked what PD & with whom he had spoken to. The male hung up the phone immediately.
I have made repeated calls to the number for this scammer after he hung up. All have gone directly to the voicemail & message noted above. I've also provided the number to several of my colleagues who have been calling it with the same results.
In the event you have been contacted by this person please report it to the CMPD at 704-336-7600. The number this "person" was calling from is 704-292-4414.
704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414
I returned the call several times. Each time the phone rang three (3) times before giving me a message stating "The person you are calling has a voicemail box that has not been set up." This morning I spoke with a person with the CMPD. They confirmed that Det. Garry McFadden was a detective in their department but has retired because he has a show on Investigation Discovery. The person indicated this is a scam and forwarded me to their Fraud Dept.
Earlier today I spoke with the person claiming to be Det. McFadden. He went into a high pressure spiel about charges being filed if I did not take care of this matter immediately. I confirmed his name & asked if he was still with the CMPD. The male stated he was. I then asked if he was the same Det. McFadden who now has a show on ID. He said that was him & he is now a private investigator. At this point I asked if he was a private investigator & no longer associated with the CMPD why was he misrepresenting himself as an officer of the law? The male did not answer this question, instead he stated that he had "talked to some people up in my area." I asked what PD & with whom he had spoken to. The male hung up the phone immediately.
I have made repeated calls to the number for this scammer after he hung up. All have gone directly to the voicemail & message noted above. I've also provided the number to several of my colleagues who have been calling it with the same results.
In the event you have been contacted by this person please report it to the CMPD at 704-336-7600. The number this "person" was calling from is 704-292-4414.
704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414 / 704-292-4414
Leaked document reveals Facebook conducted research to target emotionally vulnerable and insecure youth
From news.com.au:
Leaked document reveals Facebook conducted research to target emotionally vulnerable and insecure youth
"FACEBOOK has come under fire over revelations it is targeting potentially vulnerable youths who “need a confidence boost” to facilitate predatory advertising practices.
The allegation was revealed this morning by The Australian which obtained internal documents from the social media giant which reportedly show how Facebook can exploit the moods and insecurities of teenagers using the platform for the potential benefit of advertisers."
Leaked document reveals Facebook conducted research to target emotionally vulnerable and insecure youth
"FACEBOOK has come under fire over revelations it is targeting potentially vulnerable youths who “need a confidence boost” to facilitate predatory advertising practices.
The allegation was revealed this morning by The Australian which obtained internal documents from the social media giant which reportedly show how Facebook can exploit the moods and insecurities of teenagers using the platform for the potential benefit of advertisers."
FTC Offers ID Theft Victims Online Crime Reporting Tool
From Dark Reading:
FTC Offers ID Theft Victims Online Crime Reporting Tool
"ID theft victims can report their cybercrime attack to the Federal Trade Commission, without having to file a police report in most cases.
ID theft victims now have an alternative to filing a police report, a self-service online reporting tool from the Federal Trade Commission (FTC)."
FTC Offers ID Theft Victims Online Crime Reporting Tool
"ID theft victims can report their cybercrime attack to the Federal Trade Commission, without having to file a police report in most cases.
ID theft victims now have an alternative to filing a police report, a self-service online reporting tool from the Federal Trade Commission (FTC)."
Google, Facebook Swindled in $100M Payment Scam
From Dark Reading:
Google, Facebook Swindled in $100M Payment Scam
"Lithuanian man impersonated an Asian-based manufacturer to trick Facebook and Google into paying him $100 million.
A new investigation has uncovered details of a payment scam targeting Facebook and Google, Fortune reports. Lithuanian Evaldas Rimasauskas impersonated an Asian-based manufacturer, which often did business with both companies, to trick them into paying for products."
Google, Facebook Swindled in $100M Payment Scam
"Lithuanian man impersonated an Asian-based manufacturer to trick Facebook and Google into paying him $100 million.
A new investigation has uncovered details of a payment scam targeting Facebook and Google, Fortune reports. Lithuanian Evaldas Rimasauskas impersonated an Asian-based manufacturer, which often did business with both companies, to trick them into paying for products."
10 Cybercrime Myths that Could Cost You Millions
From Dark Reading:
10 Cybercrime Myths that Could Cost You Millions
"Don't let a cybersecurity fantasy stop you from building the effective countermeasures you need to protect your organization from attack.
Cybercrime is all over the place, with damages, according to one estimate by Cybersecurity Ventures, expected to double from $3 trillion in 2015 to $6 trillion by 2021. In a prominent 2016 ransom attack, according to the 2016 McAfee Threat Report, a criminal was supposedly able to pocket $121 million within just six months, netting $94 million after expenses. Still, too often people believe in myths that prevent them from building effective countermeasures. Here are some examples:"
10 Cybercrime Myths that Could Cost You Millions
"Don't let a cybersecurity fantasy stop you from building the effective countermeasures you need to protect your organization from attack.
Cybercrime is all over the place, with damages, according to one estimate by Cybersecurity Ventures, expected to double from $3 trillion in 2015 to $6 trillion by 2021. In a prominent 2016 ransom attack, according to the 2016 McAfee Threat Report, a criminal was supposedly able to pocket $121 million within just six months, netting $94 million after expenses. Still, too often people believe in myths that prevent them from building effective countermeasures. Here are some examples:"
New OWASP Top 10 Reveals Critical Weakness in Application Defenses
From Dark Reading:
New OWASP Top 10 Reveals Critical Weakness in Application Defenses
"It's time to move from a dependence on the flawed process of vulnerability identification and remediation to a two-pronged approach that also protects organizations from attacks.
When I wrote the first OWASP Top 10 list in 2002, the application security industry was shrouded in darkness. The insight that a few other engineers and I had gained through hand-to-hand combat with a wide variety of applications lived only within us. We recognized that for the industry to have a future, we had to make our knowledge public."
New OWASP Top 10 Reveals Critical Weakness in Application Defenses
"It's time to move from a dependence on the flawed process of vulnerability identification and remediation to a two-pronged approach that also protects organizations from attacks.
When I wrote the first OWASP Top 10 list in 2002, the application security industry was shrouded in darkness. The insight that a few other engineers and I had gained through hand-to-hand combat with a wide variety of applications lived only within us. We recognized that for the industry to have a future, we had to make our knowledge public."
FCC: net neutrality is ‘politically motivated government overreach’
From Sophos Naked Security:
FCC: net neutrality is ‘politically motivated government overreach’
"The push to weaken net neutrality that began shortly after President Trump took office took another step forward this week, with Federal Communications Commission chairman Ajit Pai announcing plans to demolish the 2015 rules former President Obama used to implement net neutrality with Title II classification."
FCC: net neutrality is ‘politically motivated government overreach’
"The push to weaken net neutrality that began shortly after President Trump took office took another step forward this week, with Federal Communications Commission chairman Ajit Pai announcing plans to demolish the 2015 rules former President Obama used to implement net neutrality with Title II classification."
Discovery of 8,800 servers sends warning to Asian cybercriminals
From Sophos Naked Security:
Discovery of 8,800 servers sends warning to Asian cybercriminals
You read that correctly. Interpol hasn’t disrupted these servers, merely passed information on their whereabouts and malevolent purpose to police forces in eight countries, including Malaysia, Myanmar, Philippines, Singapore, Thailand and Vietnam."
Discovery of 8,800 servers sends warning to Asian cybercriminals
You read that correctly. Interpol hasn’t disrupted these servers, merely passed information on their whereabouts and malevolent purpose to police forces in eight countries, including Malaysia, Myanmar, Philippines, Singapore, Thailand and Vietnam."
Lawmaker calls on ISPs to stop customers being hit by viruses
From Sophos Naked Security:
Lawmaker calls on ISPs to stop customers being hit by viruses
"Should your ISP play a greater role in keeping you safe from malware, viruses and other web threats? One of Australia’s senior politicians seems to think so. In a column in The West Australian, Dan Tehan, Australia’s cybersecurity minister, wrote: “Just as we trust banks to hold our money, just as we trust doctors with our health, in a digital age we need to be able to trust telecommunications companies to protect our information from threats.”
Lawmaker calls on ISPs to stop customers being hit by viruses
"Should your ISP play a greater role in keeping you safe from malware, viruses and other web threats? One of Australia’s senior politicians seems to think so. In a column in The West Australian, Dan Tehan, Australia’s cybersecurity minister, wrote: “Just as we trust banks to hold our money, just as we trust doctors with our health, in a digital age we need to be able to trust telecommunications companies to protect our information from threats.”
Facebook admits it is being used as propaganda tool by ‘malicious actors’
From Sophos Naked Security:
Facebook admits it is being used as propaganda tool by ‘malicious actors’
"What is Facebook?
To most people, it’s something called a “social network”, a thriving digital hub that conveniently also packages news, secure messaging, live video streaming and even a jobs marketplace.
For naysayers, it’s more like an unregulated surveillance system people might not be so keen on if they were to think about the extent to which it is constantly mining their online lives for commercial gain."
Facebook admits it is being used as propaganda tool by ‘malicious actors’
"What is Facebook?
To most people, it’s something called a “social network”, a thriving digital hub that conveniently also packages news, secure messaging, live video streaming and even a jobs marketplace.
For naysayers, it’s more like an unregulated surveillance system people might not be so keen on if they were to think about the extent to which it is constantly mining their online lives for commercial gain."
Subscribe to:
Posts (Atom)